1. CONVERT THE DECIMAL NUMBER 231 INTO ITS BINARY EQUIVALENT. SELECT THE CORRECT ANSWER FROM THE LIST BELOW.11110010
11011011
11110110
11100111*
11100101
2. CONVERT THE BINARY NUMBER 10111010 INTO ITS HEXADECIMAL EQUIVALENT. SELECT THE CORRECT ANSWER FROM THE LIST BELOW.
85
90
BA*
A1
B3
1C
3. THE FAILURE RATE IN A CERTAIN BRAND OF NETWORK INTERFACE CARD HAS BEEN DETERMINED TO BE 15%. HOW MANY CARDS COULD BE EXPECTED TO FAIL IN A COMPANY THAT HAS 80 OF THE CARDS INSTALLED?
8
10
12*
15
4. A LOCAL REAL ESTATE COMPANY CAN HAVE ITS 25 COMPUTER SYSTEMS UPGRADED FOR $1000. IF THE COMPANY CHOOSES ONLY TO UPGRADE 10 SYSTEMS, HOW MUCH WILL THE UPGRADE COST IF THE SAME RATE IS USED?
$100
$200
$400*
$500
$600
5. WHICH TWO DEVICES PROVIDE PERMANENT DATA STORAGE? (CHOOSE TWO.)
Blu-Ray disc*
hard drive*
keyboard
monitor
RAM
6. IF A TECHNICIAN USES AN AVERAGE OF 2 CANS OF COMPRESSED AIR PER WEEK FOR CLEANING, HOW MANY CANS SHOULD BE ORDERED FOR 8 TECHNICIANS OVER THE NEXT 10 WEEKS?
16
20
80
160*
200
7. WHAT IS A FUNCTION OF THE BIOS?
enables a computer to connect to a network
provides temporary data storage for the CPU
performs a power-on self test of internal components*
provides graphic capabilities for games and applications
8. WHICH IS A CHARACTERISTIC OF THE INTERNET?
It is not centrally governed.*
It uses only physical addresses.
It uses private IP addressing.
It is localized to specific geographic locations.
9. WHICH COMMAND CAN BE USED TO TEST CONNECTIVITY BETWEEN TWO COMPUTERS THAT ARE ATTACHED TO A NETWORK?
ipconfig
ping*
winipcfg
ifconfig
nbtstst -s
10. A PERSON-HOUR IS THE AMOUNT OF WORK THAT THE AVERAGE WORKER CAN DO IN ONE HOUR. IT IS ANTICIPATED THAT A COMPANY-WIDE SYSTEM UPGRADE WILL TAKE APPROXIMATELY 60 PERSON-HOURS TO COMPLETE. HOW LONG WILL IT TAKE FIVE TECHNICIANS TO PERFORM THE REFRESH?
5 hours
8 hours
10 hours
12 hours*
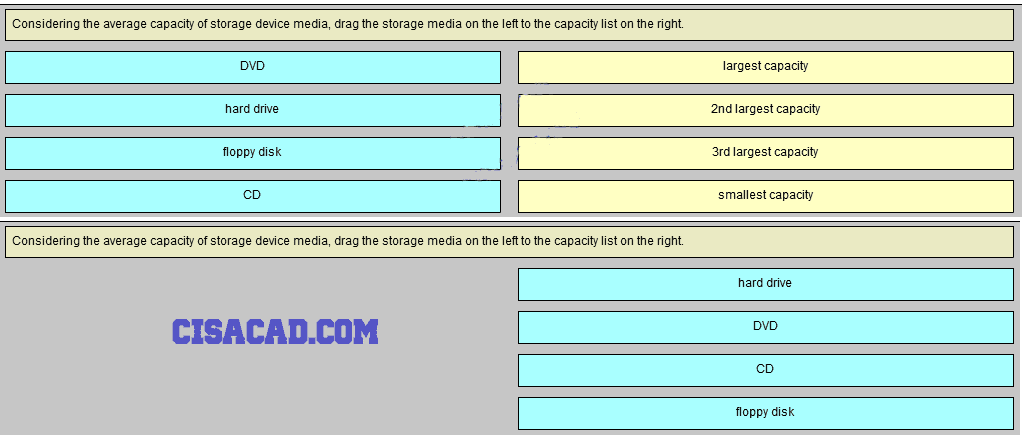
11. CONSIDERING THE AVERAGE CAPACITY OF STORAGE DEVICE MEDIA, DRAG THE STORAGE MEDIA ON THE LEFT TO THE CAPACITY LIST ON THE RIGHT.
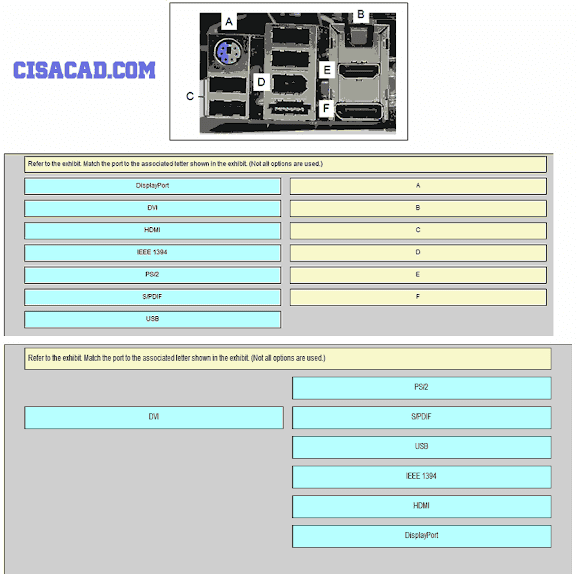
12. REFER TO THE EXHIBIT. MATCH THE PORT TO THE ASSOCIATED LETTER SHOWN IN THE EXHIBIT. (NOT ALL OPTIONS ARE USED.)
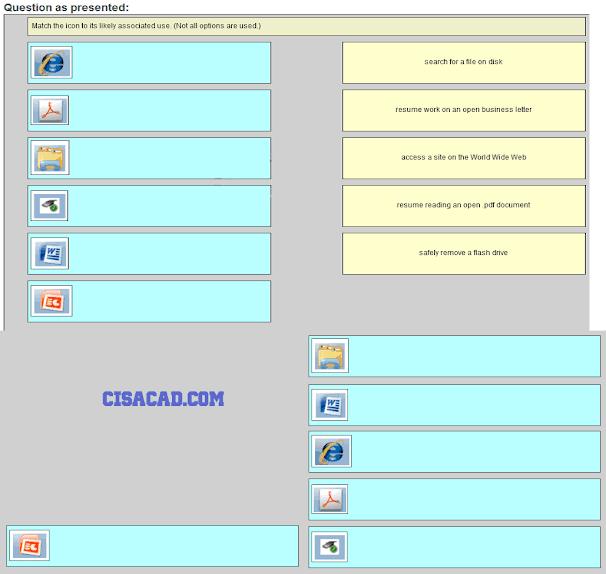
13. MATCH THE ICON TO ITS LIKELY ASSOCIATED USE. (NOT ALL OPTIONS ARE USED.)
14. MATCH THE FORM OF NETWORK COMMUNICATION WITH ITS DESCRIPTION. (NOT ALL OPTIONS ARE USED.)
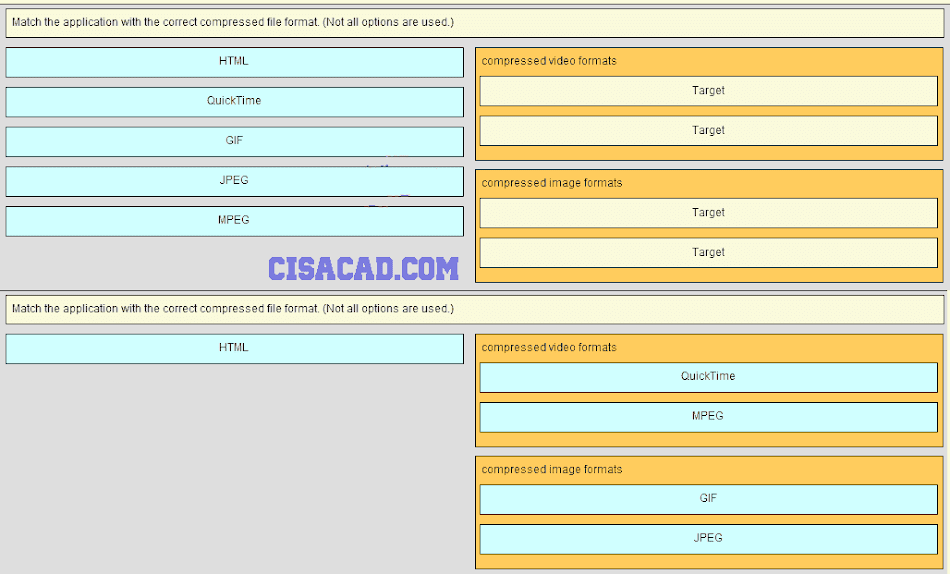
15. MATCH THE APPLICATION WITH THE CORRECT COMPRESSED FILE FORMAT. (NOT ALL OPTIONS ARE USED.)
16. A USER IS HAVING PROBLEMS ACCESSING THE INTERNET. THE COMMAND PING WWW.CISCO.COM FAILS. HOWEVER, PINGING THE IP ADDRESS OF CISCO.COM WITH THE COMMAND PING 198.133.219.25 IS SUCCESSFUL. WHAT IS THE PROBLEM?
The web server is down.
The default gateway is incorrect.
There is a problem with DNS.*
The address of the ARP cache is incorrect.
17. WHICH OPTION SHOWS THE PROPER NOTATION FOR AN IPV6 ADDRESS?
2001,0db8,3c55,0015,abcd,ff13
2001-0db8-3c55-0015-abcd-ff13
2001.0db8.3c55.0015.abcd.ff13
2001:0db8:3c55:0015::abcd:ff13*
18. WHAT IS THE PURPOSE OF THE ROUTING PROCESS?
to encapsulate data that is used to communicate across a network
to select the paths that are used to direct traffic to destination networks*
to convert a URL name into an IP address
to provide secure Internet file transfer
to forward traffic on the basis of MAC addresses
19. WHICH DEVICE SHOULD BE USED FOR ENABLING A HOST TO COMMUNICATE WITH ANOTHER HOST ON A DIFFERENT NETWORK?
switch
hub
router*
host
20. A HOME USER IS LOOKING FOR AN ISP CONNECTION THAT PROVIDES HIGH SPEED DIGITAL TRANSMISSION OVER REGULAR PHONE LINES. WHAT ISP CONNECTION TYPE SHOULD BE USED?
DSL*
dial-up
satellite
cell modem
cable modem
21. A COMPANY IS EXPANDING ITS BUSINESS TO OTHER COUNTRIES. ALL BRANCH OFFICES MUST REMAIN CONNECTED TO CORPORATE HEADQUARTERS AT ALL TIMES. WHICH NETWORK TECHNOLOGY IS REQUIRED TO SUPPORT THIS REQUIREMENT?
LAN
MAN
WAN*
WLAN
22. WHY WOULD A NETWORK ADMINISTRATOR USE THE TRACERT UTILITY?
to determine the active TCP connections on a PC
to check information about a DNS name in the DNS server
to identify where a packet was lost or delayed on a network*
to display the IP address, default gateway, and DNS server address for a PC
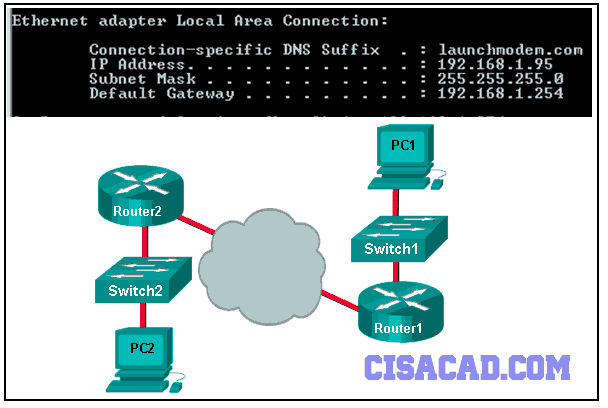
23. REFER TO THE EXHIBIT. CONSIDER THE IP ADDRESS CONFIGURATION SHOWN FROM PC1. WHAT IS A DESCRIPTION OF THE DEFAULT GATEWAY ADDRESS?
It is the IP address of the Router1 interface that connects the company to the Internet.
It is the IP address of the Router1 interface that connects the PC1 LAN to Router1.*
It is the IP address of Switch1 that connects PC1 to other devices on the same LAN.
It is the IP address of the ISP network device located in the cloud.
24. WHICH SUBNET WOULD INCLUDE THE ADDRESS 192.168.1.96 AS A USABLE HOST ADDRESS?
192.168.1.64/26*
192.168.1.32/27
192.168.1.32/28
192.168.1.64/29
25. A TECHNICIAN USES THE PING 127.0.0.1 COMMAND. WHAT IS THE TECHNICIAN TESTING?
the TCP/IP stack on a network host*
connectivity between two adjacent Cisco devices
connectivity between a PC and the default gateway
connectivity between two PCs on the same network
physical connectivity of a particular PC and the network
26. WHAT IS THE PURPOSE OF ICMP MESSAGES?
to inform routers about network topology changes
to ensure the delivery of an IP packet
to provide feedback of IP packet transmissions*
to monitor the process of a domain name to IP address resolution
27. WHAT IS THE GENERAL TERM THAT IS USED TO DESCRIBE A PIECE OF DATA AT ANY LAYER OF A NETWORKING MODEL?
frame
packet
protocol data unit*
segment
28. HOW DOES A NETWORKED SERVER MANAGE REQUESTS FROM MULTIPLE CLIENTS FOR DIFFERENT SERVICES?
The server sends all requests through a default gateway.
Each request is assigned source and destination port numbers.*
The server uses IP addresses to identify different services.
Each request is tracked through the physical address of the client.
29. WHICH PROTOCOL TRANSLATES A WEBSITE NAME SUCH AS WWW.CISCO.COM INTO A NETWORK ADDRESS?
HTTP
FTP
DHCP
DNS*
30. A NETWORK TECHNICIAN IS ATTEMPTING TO CONFIGURE AN INTERFACE BY ENTERING THE FOLLOWING COMMAND: SANJOSE(CONFIG)# IP ADDRESS 192.168.2.1 255.255.255.0. THE COMMAND IS REJECTED BY THE DEVICE. WHAT IS THE REASON FOR THIS?
The command is being entered from the wrong mode of operation.*
The command syntax is wrong.
The subnet mask information is incorrect.
The interface is shutdown and must be enabled before the switch will accept the IP address.
31. WHAT PROTOCOL IS RESPONSIBLE FOR CONTROLLING THE SIZE OF SEGMENTS AND THE RATE AT WHICH SEGMENTS ARE EXCHANGED BETWEEN A WEB CLIENT AND A WEB SERVER?
TCP*
IP
HTTP
Ethernet
32. A NETWORK ADMINISTRATOR IS TROUBLESHOOTING CONNECTIVITY ISSUES ON A SERVER. USING A TESTER, THE ADMINISTRATOR NOTICES THAT THE SIGNALS GENERATED BY THE SERVER NIC ARE DISTORTED AND NOT USABLE. IN WHICH LAYER OF THE OSI MODEL IS THE ERROR CATEGORIZED?
presentation layer
network layer
physical layer*
data link layer
33. WHICH STATEMENT IS TRUE ABOUT VARIABLE-LENGTH SUBNET MASKING?
Each subnet is the same size.
The size of each subnet may be different, depending on requirements.*
Subnets may only be subnetted one additional time.
Bits are returned, rather than borrowed, to create additional subnets.
34. A WIRELESS HOST NEEDS TO REQUEST AN IP ADDRESS. WHAT PROTOCOL WOULD BE USED TO PROCESS THE REQUEST?
FTP
HTTP
DHCP*
ICMP
SNMP
35. WHAT WILL A HOST ON AN ETHERNET NETWORK DO IF IT RECEIVES A FRAME WITH A DESTINATION MAC ADDRESS THAT DOES NOT MATCH ITS OWN MAC ADDRESS?
It will discard the frame.*
It will forward the frame to the next host.
It will remove the frame from the media.
It will strip off the data-link frame to check the destination IP address.
36. WHICH CONNECTION PROVIDES A SECURE CLI SESSION WITH ENCRYPTION TO A CISCO SWITCH?
a console connection
an AUX connection
a Telnet connection
an SSH connection*
37. WHAT ARE THE THREE RANGES OF IP ADDRESSES THAT ARE RESERVED FOR INTERNAL PRIVATE USE? (CHOOSE THREE.)
10.0.0.0/8*
64.100.0.0/14
127.16.0.0/12
172.16.0.0/12*
192.31.7.0/24
192.168.0.0/16*
38. WHAT STATEMENT DESCRIBES THE FUNCTION OF THE ADDRESS RESOLUTION PROTOCOL?
ARP is used to discover the IP address of any host on a different network.
ARP is used to discover the IP address of any host on the local network.
ARP is used to discover the MAC address of any host on a different network.
ARP is used to discover the MAC address of any host on the local network.*
39. WHAT IS THE PURPOSE OF HAVING A CONVERGED NETWORK?
to provide high speed connectivity to all end devices
to make sure that all types of data packets will be treated equally
to achieve fault tolerance and high availability of data network infrastructure devices
to reduce the cost of deploying and maintaining the communication infrastructure*
40. REFER TO THE EXHIBIT. MATCH THE PACKETS WITH THEIR DESTINATION IP ADDRESS TO THE EXITING INTERFACES ON THE ROUTER. (NOT ALL TARGETS ARE USED.)